*Post written with my coauthor Ryan Maness. We are currently rounding the corner and almost ready to submit the final version of our Cyber Conflict book. This post represents ongoing research as we fill out unanswered questions in our text.
My coauthor and I have dissected the contemporary nature of cyber conflict in many ways, from cataloging all actual cyber incidents and disputes between states, to examining cyber espionage, and finally, examining the impact of cyber incidents on the conflict-cooperation nexus of states. What we have not done until now is examine the nature of what we call cyber spillover. 
Cyber spillover is when cyber conflicts seep and bleed into traditional arena of militarized and foreign policy conflict. While it is dubious to claim that the cyber domain is disconnected from the physical domain given that cyber technology has to be housed somewhere, it is also true that there are very few incidents of cyber actions causing physical damage (the only case being Stuxnet). Our question is not about the transition from cyber to physical, but when cyber disagreements lead directly to conventional foreign policy disputes between states, thus altering how international interactions work.
The claim is that the cyber era is different and we will see drastically new dynamics evident in the international discourse. If true then, we would often see cyber conflicts and events transition from the digital realm to the normal international realm. I have heard this claim made repeatedly at cyber conferences. We decided to examine the empirical veracity of these claims.
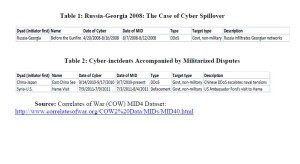
The data demonstrates a bit of a different story. In our dataset there are 110 cyber incidents between states from 2001 to 2011. We find that only three of these incidents are connected to further international tensions under what we might consider a Militarized Interstate Dispute (MID), a use, display, or threat of force (using the newly released MID 4.01 data). We find only one incident that actually precedes a militarized interstate dispute. This took place in 2008, with perhaps the most well known case of cyber actions during a militarized campaign was the series of defacements and DDoS incidents conducted by Russia against Georgia during the August 2008 five-day conflict. However, the claim that these cyber actions led directly to this military campaign is dubious at best. The militarized campaign did not need the preceding cyber incident to succeed, and the primary purpose of the cyber portion of the Russian campaign was to instill fear and confusion within the Georgian government and people. The cyber dispute in and of itself did not cause the conventional conflict.
The two other militarized disputes involving cyber did not have cyber incidents preceding the militarized ones; therefore evidence for cyber spillover as becoming part of relations among rivals is on shaky ground. One incident involves Japan and China in the continuing displays of force between the two rivals over territorial concerns in the East China Sea. We find that when a cyber incident seeps into the conventional international affairs battlefield, the reason is likely because the disputes are connected to territorial issues that are likely to be very salient between the two parties.
The other incident on our list is the one between the US and Syria. On that occasion, in reaction to the visit by US Ambassador to Syria John Ford to the besieged city of Hama in the beginnings of the bloody civil war, the Syrian government initiated a short series of anti-American defacements on the US State Department’s official webpage. What followed was an escalation of violence in the city initiated by Syrian government forces against rebel combatants and civilians in that city.
There are obvious caveats evident from this work. One might be that we have only seen the beginnings of cyber conflict therefore we cannot make claims about the future of cyber conflict and spillover because the future is evolving. While the future of cyber conflict is developing, we do have quite a bit of evidence so far of how cyber actors interact so far. The history from 2001 to 2011 is evident by our data, add to that no real evidence of cyber spillover to the present date and we have a wide range of data available to make predictions.
It is also probable that future uses of a technology are often dictated by how the factor is used early on its development. We often see this process with technological developments, what is acceptable is often determined early in the life of a technology. Take for example nuclear weapons, they were used early in their life cycle and the reaction was so immediate against future usage that a norm against the technology developed. On the other hand, other technologies like machine guns, tanks, ballistic missiles were deployed and used widely early.
We shall see what the cyber future brings but so far our work has demonstrated that states have been restrained in the use of cyber technology. Here we demonstrate that states are mostly restrained from transitioning a cyber threat to a physical threat. This calls into question cyber revolution hypothesis, the idea that cyber conflict will change how interactions take place. If anything, cyber seems to reinforce typical international patterns rather than be a pathway for new patterns.
Valeriano serves as the Donald Bren Chair of Military Innovation at the Marine Corps University.His work also includes serving as a Senior Fellow at the Cato Institute and as Senior Advisor to the Cyberspace Solarium Commission.


0 Comments